T heir technical infrastructure hardware and software security capabilities.
Electronic security systems include all of the following except which of the below.
Technological advances quickly antiquate hardware installations b.
Individuals or organizations may attempt to overload the system preventing legitimate customers from accessing the site.
Surveillance infiltration execution.
Hackers may attempt to access sensitive information c.
Costs of internet commerce include all the following except.
These measures include the following.
The costs of security measures.
Cyberstalking is the use of the internet or other electronic means to stalk or harass an individual group or organization it may also include monitoring identity theft threats vandalism solicitation for sex or gathering information that may be used to threaten embarrass or harass.
A producing a superior product and charging less than competitors.
The security rule calls this information electronic protected health information e phi.
Mailroom and other document preparation and handling costs are eliminated d.
A very prominent example will be ssl tls a security protocol for communications over the internet that has been used in conjunction with a large number of internet protocols to ensure security.
Staffing and training employees to work in a technology driven environment b.
B implementing information systems to support better management decision making.
The risks to a business of internet commerce include all of the following except.
Other ways to ensure information confidentiality include enforcing file permissions and access control list to restrict access to sensitive information.
It may seem obvious but all the security in the world is useless if an intruder can simply walk in and physically remove a computing device.
In a security classification system the level at which disclosure of information could cause exceptionally grave damage is.
C garnering more sales and profits than your competitors.
The phases of a large scale attack on an enterprise network or systems include the following except.
Data librarian in an information systems organization all of the following functions might logically report to the data center manager except.
3 the security rule does not apply to phi transmitted orally or in writing.
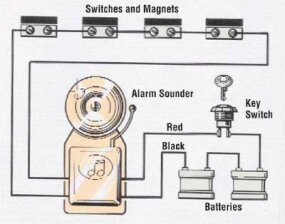
The earliest form of electronic keying was.
Organizational change to a completely different way of doing business c.
Their size complexity and capabilities.
High value information assets should be secured in a location with limited access.
All of the following choices describe ways for a company to achieve a competitive advantage except.